22 April 2021
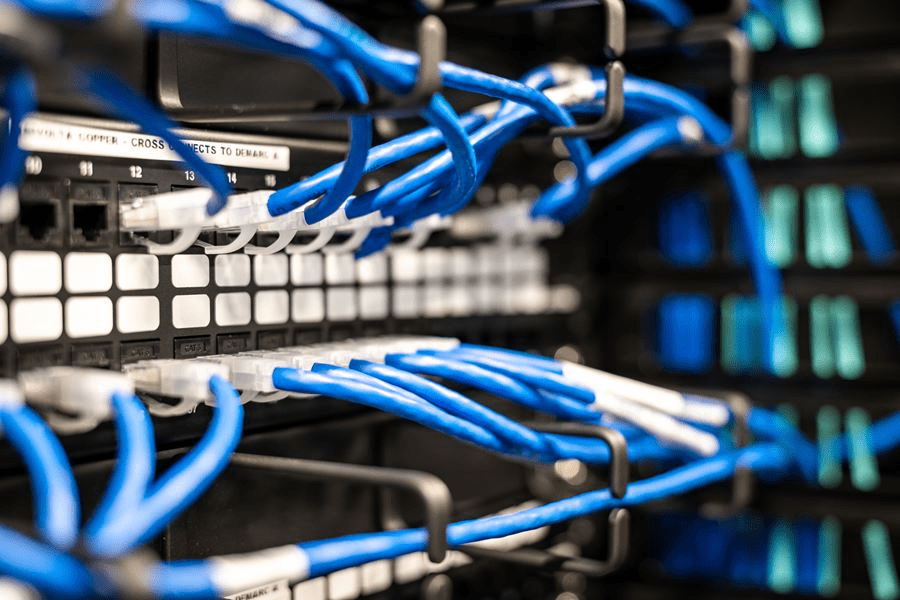
Langkah Penting untuk Mengamankan dan Membangun Infrastruktur Jaringan
Membangun infrastruktur jaringan untuk bisnis Anda dan organisasi Anda, mungkin memerlukan biaya tinggi; tetapi memiliki infrastruktur jaringan tanpa jaminan bisa lebih mahal. Memanfaatkan teknologi dapat membuat bisnis Anda lebih mudah dioperasikan.
Selain itu, kita hidup di era teknologi. Kami membutuhkan teknologi dan infrastruktur TI untuk hampir setiap bagian dari bisnis kami, baik itu untuk penelitian dan pengembangan, mengelola data besar, hingga pemasaran dan promosi.
Infrastruktur TI yang tepat bukan hanya tentang alat dan layanan yang dapat kita manfaatkan; Pentingnya infrastruktur jaringan canggih adalah semua tentang keamanan dan menghindari kesalahan.
Masalah tersebut dapat disebabkan oleh kurangnya pengetahuan organisasi Anda tentang kesalahan keamanan atau teknologi. Memiliki rencana dan langkah-langkah praktis untuk infrastruktur jaringan penting dapat membantu Anda mengurangi masalah yang berasal dari penggunaan teknologi.
Ada beberapa komponen untuk memeriksa dan mengevaluasi jaringan Anda agar tetap aman. Berikut adalah beberapa langkah untuk membangun infrastruktur jaringan, dan untuk memelihara dan mengamankan jaringan TI Anda:
1. Penilaian/Audit Keamanan Jaringan
Audit keamanan jaringan adalah proses di mana perusahaan menyelidiki dan menilai jaringan mereka untuk mengidentifikasi setiap kekurangan potensial yang menyebabkan kompromi / pelanggaran keamanan.
Penilaian dapat diselesaikan oleh tim cybersecurity internal atau dengan mempekerjakan pihak ketiga untuk diaudit. Potensi masalah akan datang dari kebijakan keamanan jaringan dan berbagai aset yang ada di jaringan.
Audit komprehensif mencakup hampir semua proses peninjauan komponen seperti arsitektur / konfigurasi firewall, identifikasi aset, kebijakan / prosedur keamanan, penilaian risiko.
Dalam proses ini, auditor harus memperbarui pengetahuan mereka tentang kebijakan keamanan yang diperbarui, perangkat lunak, sistem operasi, pengguna atau anggota jaringan. Data yang diperbarui akan membantu Anda memiliki infrastruktur jaringan yang lebih baik.
2. Melakukan Pelatihan Kesadaran Keamanan Siber
Pengetahuan tentang keamanan tidak hanya untuk tim cybersecurity atau staf TI, tetapi juga untuk semua karyawan Anda.
Terkadang, masalah datang dari karyawan yang tidak menyadari apa yang mereka lakukan dalam infrastruktur jaringan perusahaan. Mereka dapat berselancar di browser, mendaftar atau masuk untuk sesuatu yang dapat menjadi ancaman bagi organisasi.
Namun, Harvard Business Review menyatakan bahwa 60% dari semua serangan jaringan dilakukan oleh orang dalam. Meskipun serangan dan masalah mungkin datang dari dalam, itu tidak berarti mereka selalu tahu kesalahan mereka.
Anda dapat meningkatkan kesadaran dalam hal-hal dasar seperti membuat kata sandi untuk ponsel atau laptop mereka, terutama jika mereka memiliki data dan akun perusahaan di gadget mereka.
3. Batasi Akses Pengguna
Kebijakan hak istimewa paling tidak (POLP) dapat menjadi solusi Anda untuk membatasi akses anggota. Dengan POLP, pengguna di jaringan Anda dibatasi untuk memiliki tingkat akses minimum berdasarkan fungsi pekerjaan inti mereka. Metode ini dapat membantu Anda mengurangi risiko orang dalam mencuri data.
Selain POLP, Anda dapat memisahkan jaringan tamu dari jaringan utama. Jaringan utama mungkin untuk karyawan dan jaringan tamu untuk tamu atau mitra bisnis yang membutuhkan akses Wi-Fi ketika mereka berada di kantor Anda.
4. Back-up Data Anda
Kami tidak pernah tahu kapan dan bagaimana serangan akan terjadi. Memiliki cadangan data dapat membantu dalam upaya pemulihan data Anda. Ini bisa lebih baik jika Anda mencadangkan data Anda pada layanan cloud, karena memungkinkan Anda untuk menyimpan cadangan terenkripsi.
Anda bisa mengaksesnya kapan saja. Jangan lupa untuk menguji layanan cadangan Anda secara teratur untuk mencegah masalah yang mencegah Anda mengakses data Anda di masa-masa kritis.
5. Memperbarui Perangkat Lunak Anti-Virus Anda
Anti-virus adalah suatu keharusan untuk infrastruktur jaringan. Saat ini, virus dan malware lebih berkembang dan mudah beradaptasi untuk menyerang jaringan Anda.
Di sisi lain, perusahaan anti-virus selalu memperbarui layanan mereka untuk mencegah virus atau malware terbaru.
Ketika Anda memahami langkah-langkah penting untuk menyimpan jaringan Anda, Anda dapat mencegah serangan. Inisiatif dapat berasal dari staf TI internal Anda, atau beberapa perusahaan mengalihdayakan pihak ketiga untuk mengelola jaringan mereka.
Pastikan bahwa perusahaan Anda memiliki langkah-langkah ini juga, atau beberapa peraturan keamanan jaringan. Semakin aman jaringan Anda, semakin aman data Anda, terutama untuk bisnis Anda.
Apakah informasi ini membantu?