09 November 2022
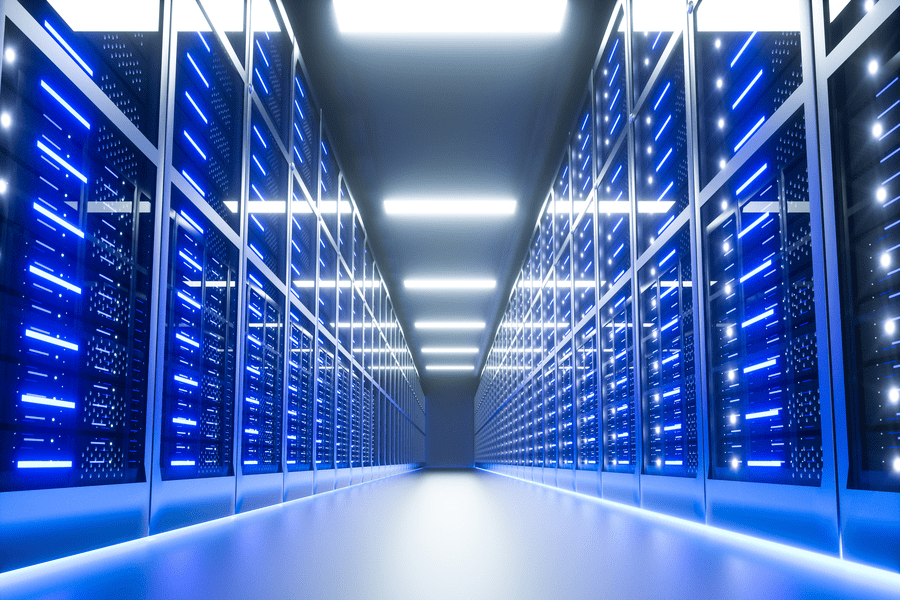
Amankan Data Anda dengan Infrastruktur Cloud dan Pusat Data
Data sangat penting untuk industri teknologi. Tapi, tanpa keamanan yang baik, itu bisa dicuri. Tujuan utama pengembangan layanan internet adalah untuk kemudahan transfer data. Di masa lalu, perusahaan memiliki pusat data kecil mereka sendiri di mana mereka akan menyimpan data mereka dan menjalankan server. Namun, sekarang ada ketersediaan komputasi awan dan infrastruktur pusat data yang sangat besar yang membuat ini jauh lebih baik.
Cloud menawarkan keamanan yang lebih baik dan otentikasi multi-faktor, membuat peretasan jauh lebih sulit. Pusat data juga memiliki infrastruktur yang baik untuk meningkatkan transmisi, manajemen, dan penyimpanan data. Artikel ini membawa Anda melalui beberapa ancaman dan kerentanan data yang signifikan dan bagaimana bisnis menggunakan pusat data dan infrastruktur cloud untuk menghindarinya.
Ancaman dan kerentanan data umum
Keamanan data seringkali merupakan yang paling sulit dideteksi dan dikelola dengan keamanan data. Beberapa bisnis menghabiskan uang untuk pelatihan staf untuk mengharapkan bahwa tenaga kerja yang berpengetahuan luas, yang sadar akan dampak fiskal dan sosial dari pelanggaran keamanan siber, akan cukup untuk meningkatkan kewaspadaan dan mencegah prosedur keamanan yang buruk.
Pada kenyataannya, perusahaan seringkali hanya membutuhkan satu karyawan yang tidak bertanggung jawab untuk menyebabkan insiden keamanan yang dahsyat. Risiko orang dalam yang bermusuhan dan karyawan yang tidak bahagia yang berusaha merusak merek perusahaan atau mencuri data ketika meninggalkan perusahaan juga merupakan kemungkinan konstan.
Selain itu, beberapa ancaman dan kerentanan data paling umum yang dialami perusahaan.
● Peretasan: Ini adalah salah satu cara paling umum data dapat diganggu. Ini melibatkan akses tidak sah ke data dengan mengubah sistem penyimpanan data. Peretas mendapatkan akses ke jaringan atau sistem dengan beberapa cara, beberapa serumit mengubah enkripsi program, sementara yang lain sesederhana menebak kode sandi pengguna atau menempatkan pencatat penekanan tombol.
● Kebocoran data: Ini adalah kerentanan yang melibatkan transfer data ke tujuan yang tidak sah.
● Malware: Malware mengganggu proses komputer, mengumpulkan materi rahasia, atau mendapatkan akses ke sistem jaringan untuk membahayakan data dan informasi. Perangkat lunak keamanan dan firewall biasanya digunakan untuk menjauhkan virus dari perangkat. Malware dapat berbentuk virus, bug, adware, rootkit, key-logger, dan DDoS, tetapi juga bisa berupa perangkat lunak apa pun yang berfungsi melawan kebutuhan administrator sistem.
● Advanced Persistent Threat (APT): Tujuan APT bukanlah untuk menghancurkan atau mengganggu file, tetapi untuk mengambil data saat masuk. Peretas melakukan serangan jangka panjang pada sistem komputer untuk menghindari penemuan dan mengumpulkan informasi penting.
Menggunakan Data Center & Cloud Infrastructure for Business
Dengan tingkat ketidakamanan data yang meningkat setiap hari, bisnis perlu menggunakan pusat data dan infrastruktur cloud untuk mengekang ancaman serangan dunia maya. Pusat data memastikan Anda mendapatkan manajemen data yang baik dengan semua infrastruktur untuk mengunci ancaman apa pun. Dengan cara yang sama, cloud membantu mendapatkan penyimpanan data yang aman dan tidak terbatas.
Bisnis harus memanfaatkan pusat data andal yang menawarkan layanan cloud untuk penyimpanan, manajemen, dan transfer data. Telkom DWS melalui brand-nya neuCentrIX menawarkan layanan cloud dan data center ini dengan infrastruktur teknologi yang memadai untuk bisnis Anda. Lihat situs web kami untuk mempelajari lebih lanjut tentang layanan kami.
Apakah informasi ini membantu?